Risk Management Enterprise Can Be Fun For Everyone
Wiki Article
The 9-Second Trick For Risk Management Enterprise
Table of ContentsSome Known Details About Risk Management Enterprise Some Of Risk Management EnterpriseThings about Risk Management EnterpriseSome Known Details About Risk Management Enterprise Risk Management Enterprise for DummiesRisk Management Enterprise - TruthsThe Best Guide To Risk Management Enterprise
Real-Time Threat Assessments and Reduction in this software allow organizations to continually monitor and assess dangers as they progress. When risks are determined, the software application helps with prompt mitigation activities.
KRIs resolve the problem of irregular or uncertain risk evaluation. They resolve the challenge of ongoing threat management by offering tools to check risks constantly. KRIs improve security threat oversight, guaranteeing that possible risks are determined and taken care of efficiently. The task of risk monitoring should not be a challenge. Organizations must depend on a first-class and innovative threat monitoring software program.
Some Known Questions About Risk Management Enterprise.
IT take the chance of management is a part of enterprise danger administration (ERM), created to bring IT take the chance of in line with a company's threat cravings. IT risk monitoring (ITRM) includes the policies, procedures and innovation needed to minimize dangers and vulnerabilities, while keeping compliance with suitable regulative needs. Additionally, ITRM seeks to restrict the consequences of harmful events, such as safety and security violations.Veronica Rose, ISACA board supervisor and an information systems auditor at Metropol Corp. The ISACA Danger IT framework lines up well with the COBIT 2019 framework, Rose claimed.
Venture Risk Monitoring Software Advancement: Conveniences & Characteristics, Expense. With technological improvements, dangers are constantly on the increase. That being said, companies are a lot more most likely to deal with difficulties that affect their funds, operations, and track record. From swiftly rising and fall markets to governing adjustments and cyber risks, businesses navigate through a regularly altering sea of risks.
Things about Risk Management Enterprise
In this blog site, we will certainly study the globe of ERM software application, exploring what it is, its advantages, functions, etc to ensure that you can build one for your service. Business Threat Management (ERM) software is the application program for planning, routing, organizing, and managing service tasks and improving risk management processes.With ERM, companies can make insightful choices to boost the total resilience of the organization. Devoted ERM systems are vital for organizations that regularly deal with huge quantities of sensitive info and multiple stakeholders to accept strategic decisions.
It can be stayed clear of by making use of the ERM software system. This system automates guideline conformity monitoring to maintain the company safe and certified.
The Greatest Guide To Risk Management Enterprise
You can additionally attach existing software systems to the ERM through APIs or by including data manually. Services can use ERM to assess risks based upon their potential impact for much better risk administration and mitigation.: Adding this function allows individuals to get real-time notices on their gadgets about any danger that could occur and its impact.
Rather, the software program allows them to set thresholds for different processes and send out press alerts in instance of possible threats.: By integrating data visualization and reporting in the custom-made ERM software, businesses can get clear understandings about risk fads and performance.: It is mandatory for organizations to stick to market conformity and regulatory standards.
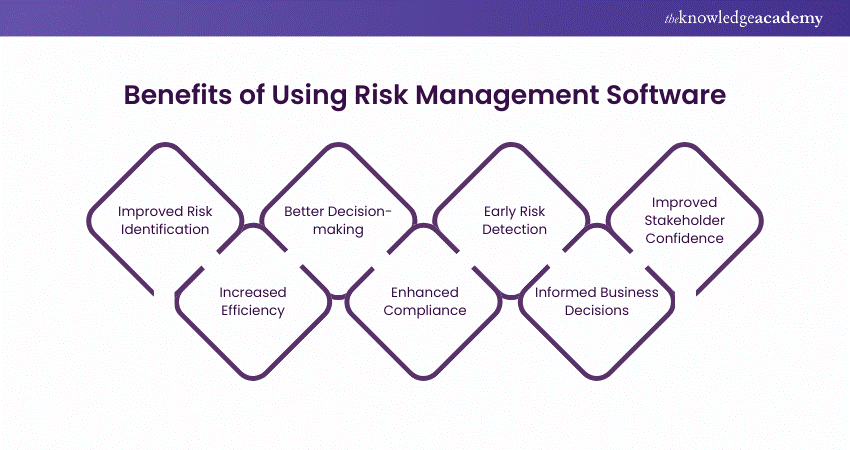
These systems enable companies to execute best-practice threat monitoring processes that line up with industry requirements, supplying an effective, technology-driven technique to determining, analyzing, and mitigating dangers. This blog explores the benefits of automatic risk monitoring devices, the areas of threat monitoring they can automate, and the worth they bring to an organization.
The Risk Management Enterprise Statements
Groups can establish forms with the appropriate areas and easily produce different kinds for different threat kinds. These threat analysis kinds can be circulated for conclusion via automated workflows that send notices to the pertinent personnel to complete the kinds online. If forms are not finished by the target date, after that chaser emails are instantly sent out by the system.The control tracking and control screening procedure can also be automated. Firms can utilize automated process to send out routine control examination notifications and team can enter the results using online kinds. Controls can also be checked by the software by setting rules to send signals based on control data held in other systems and spreadsheets that is pulled into the platform using API integrations.
Threat management automation software application can likewise support with threat reporting for all degrees of the business. Leaders can watch reports on risk direct exposure and control performance with a range of reporting results consisting of fixed reports, Power BI interactive reports, bowtie analysis, and Monte Carlo simulations. The ability to pull live records at the touch of a switch reduces out arduous data important site manipulation jobs leaving risk groups with even more time to analyze the information and recommend business on the ideal training course of activity.
Organizations operating in affordable, fast-changing markets can't manage hold-ups or ineffectiveness in dealing with potential risks. Typical risk administration utilizing manual spreadsheet-based processes, while familiar, usually lead to fragmented data, lengthy reporting, and a raised chance of human error.
See This Report about Risk Management Enterprise
This guarantees risk registers are always present and aligned with business purposes. Compliance is another critical motorist for automating risk management. Requirements like ISO 31000, CPS 230 and COSO all offer guidance around risk administration ideal techniques and control frameworks, and automated danger management devices are structured to align with these requirements helping firms to satisfy most generally made use of threat administration criteria.Look for danger software platforms with a permissions hierarchy to conveniently establish operations for danger escalation. This capability enables you to customize the view for each and every user, so they just see the information appropriate to them. Make certain the ERM software provides individual tracking so you can see who entered what information and when.
Opt for a cloud-based platform to make certain the system receives normal updates from the supplier including brand-new functionality. Look for devices that use project threat administration capabilities to manage your tasks and portfolios and the connected risks. The advantages of adopting risk monitoring automation software program expand much beyond effectiveness. Services that integrate these services right into their ERM method can expect a host of tangible and abstract.
The 6-Second Trick For Risk Management Enterprise
While the case for automation is engaging, carrying out a risk administration platform is not without its obstacles. To overcome the challenges of risk administration automation, organizations need to invest in data cleaning and governance to guarantee a strong structure for applying an automated system.Automation in danger monitoring equips companies to transform their technique to risk and construct a stronger foundation for the future (Risk Management Enterprise). The inquiry is no more whether to automate threat administration, it's how soon you can begin. To see the Riskonnect at work,
The answer frequently lies in exactly how well threats are prepared for and taken care of. Task administration software offers as the navigator in the troubled waters of project execution, offering tools that determine and examine threats and create methods to mitigate them effectively.
Report this wiki page